Booking tickets online usually follows a standard and well-honed procedure. You select the day and time of departure, the travel class, and pay to book your ticket. Thalys, the French-Belgian train operator, recently chose a revolutionary alternative: letting travellers themselves select the price, even negative, for every Thalys, TGV, or Eurostar trip. Do you want to go from London to Amsterdam and receive 1000 €? I’m in!
In April 2018, I discovered a vulnerability on the Thalys TheCard website, the Thalys loyalty platform for customers to collect miles as they travel and exchange them later for gifts or free train tickets. Online, card holders can exchange accumulated miles for tickets but also Bose sound systems, camera lenses, or PlayStation® 4.
To exchange miles for tickets, https://thalysthecard.com/en/search-reward-ticket let users select stations, date, time, and 2nd or 1st class, then book the selected train. If the user does not have enough miles (for instance, 5800 for a 1st class ticket between Belgium and France), the selected option (Brussels to Paris at 10:13 in 1st class) is disabled and cannot be clicked.
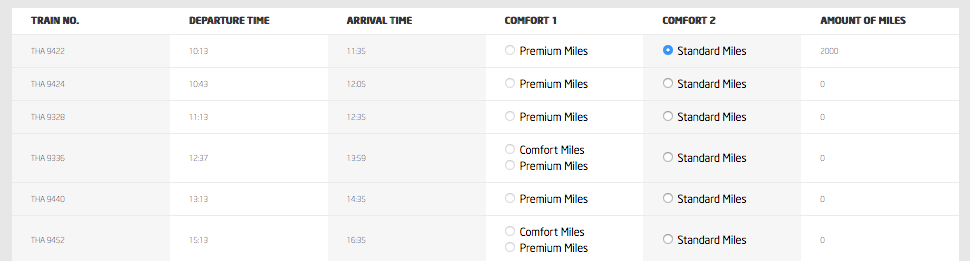
By default, the webpage only lets you redeem tickets if you have enough miles, here 2000 for a Brussels to Paris train. I cannot click on the Premium 1st class tickets since I haven’t accumulated 5800+ miles in my account.
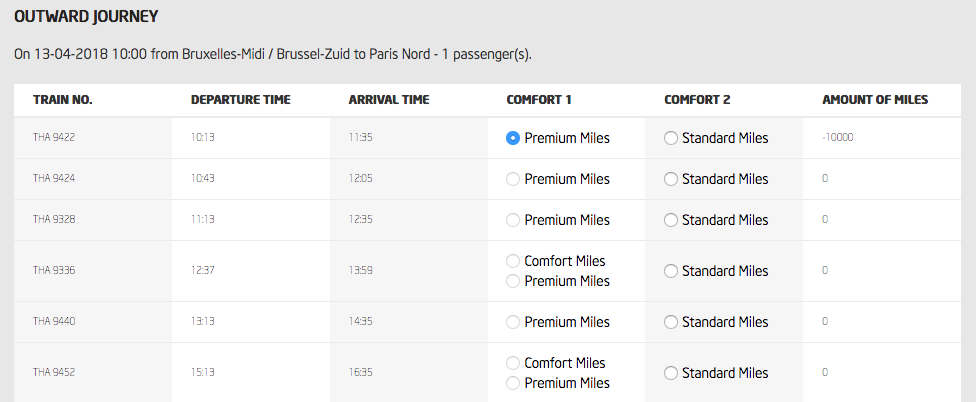
However, you can simply change the price in the browser and Thalys will trust this value. Here, a first-class ticket for minus 10000 miles.
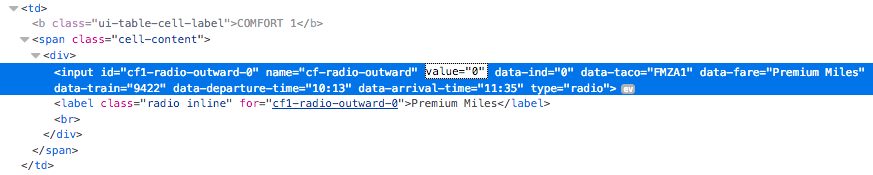
Editing the price is simple and easy; open the HTML inspector and change the value field.
Upon submission, the service uses the price submitted by the user without further verification and automatically sends a booking confirmation. That also means someone could artificially increase their miles balance by millions of miles and immediately order hundreds of PS4. Would they arrive, would this be flagged?
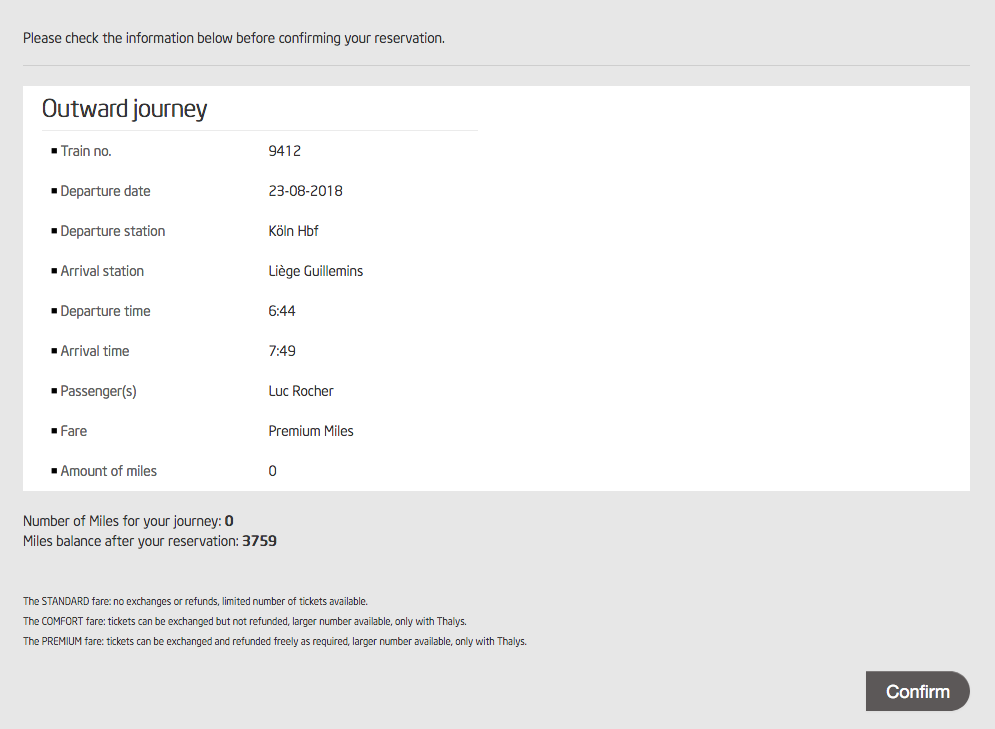
Successfully booking a Köln-Liège for 0 miles? Here’s your ticket.
Where the nightmare begins. Thalys has no contact email, no dedicated IT/security support, no free phone number. Armed with two tickets booked for 0 miles, I am, however, eager to contact Thalys and not go to jail. I ask a contact for a legal advice, who tells me I should just not contact them and forget about this. Remember Laszlo Marai who got jailed for reporting a vulnerability in the Budapest Transport Authority’s online payment website?
I decide to check with my university and, with my supervisor, we contact the Thalys CM on Twitter with a very brief description, telling them we’re happy to provide further details. A few days later, the CM simply answers they fixed the issue, removed the free tickets, and offer 1000 miles for the help, worth 1/2 of a Brussels-Paris or 1/9 of a Brussels-London. Bye.
A year later, there is still no dedicated way to report a security vulnerability to Thalys and no vulnerability disclosure policy on their website, contrary to other train operators in Europe.